How I earned 5040$ from Twitter by showing a way to Harvest other users IP address
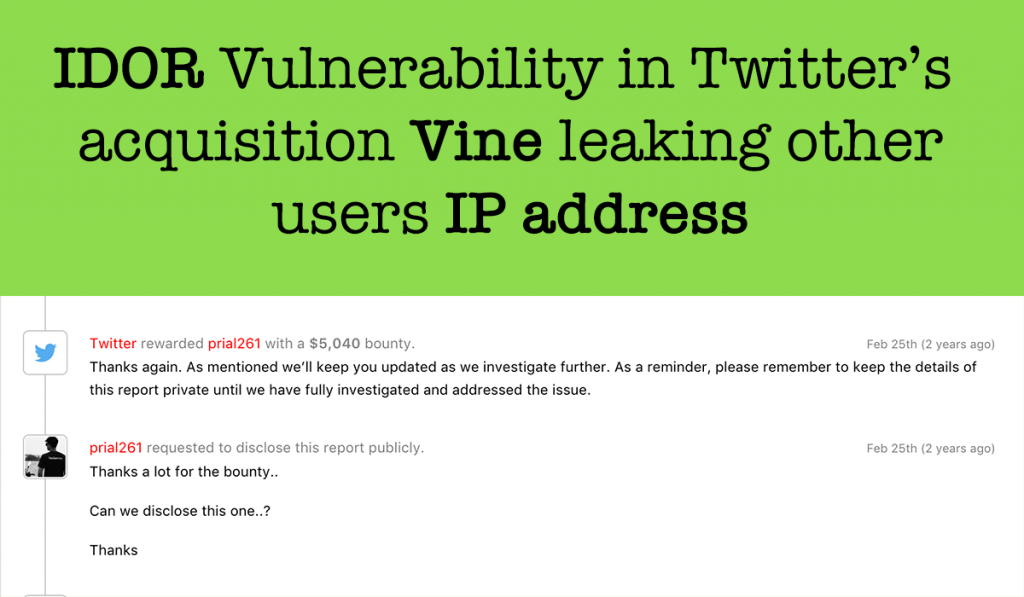
Hi guys, This is one of my old finding adding to my blog. Recently I disclosed a POC on How I was able to get all vine user’s sensitive Information including Phone no/IP Address/Emails and Many more that was reported to Twitter and they patched it and rewarded me 7560$. Those who missed it you […]
External link warning page bypass in Zerocopter

Description: zerocopter.com is a bug bounty platform for Ethical hackers just like Hackerone. In Zerocopter reports, users can use Markdown. Users are also allowed to give external links in reports. If a user clicks on the External link in reports then it takes the user to an external warning page like the below screenshot But I […]
