Bug Bounty
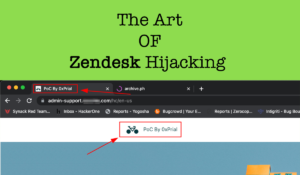
The Art Of Zendesk Hijacking
Back in July 2023, I was testing a HackerOne Private Program [ let’s call this target xyz.com ] and this target scope was pretty limited. The scope was – xyz.com admin.xyz.com api.xyz.com













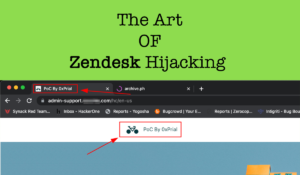
Back in July 2023, I was testing a HackerOne Private Program [ let’s call this target xyz.com ] and this target scope was pretty limited. The scope was – xyz.com admin.xyz.com api.xyz.com
First Happy new year to fellow Hackers, I was planning to write on my blog regularly for the last few months, but I could not do that due to my
Hi fellow Hackers,At first Ramadan Kareem! Wishing everyone a very happy Ramadan. Today I will write about an Insecure direct object references (IDOR) vulnerability that I recently discovered in Uber
© All Rights Reserved By Prial Islam